Split tunneling allows you to choose which traffic passes through the tunnel and which traffic bypasses the tunnel and accesses the resource directly.
Private network traffic is always tunneled through the cloud, based on your network tunnels and routing table settings.
You can specify additional destinations to route through the Check Point SASE cloud (for example, public resources that require inspection) or to bypass the tunnel.
Configuring Split Tunneling for a Network
- Access the Check Point SASE Administrator Portal and click Networks.
- Select your network.
- Click ... and click Split Tunneling.
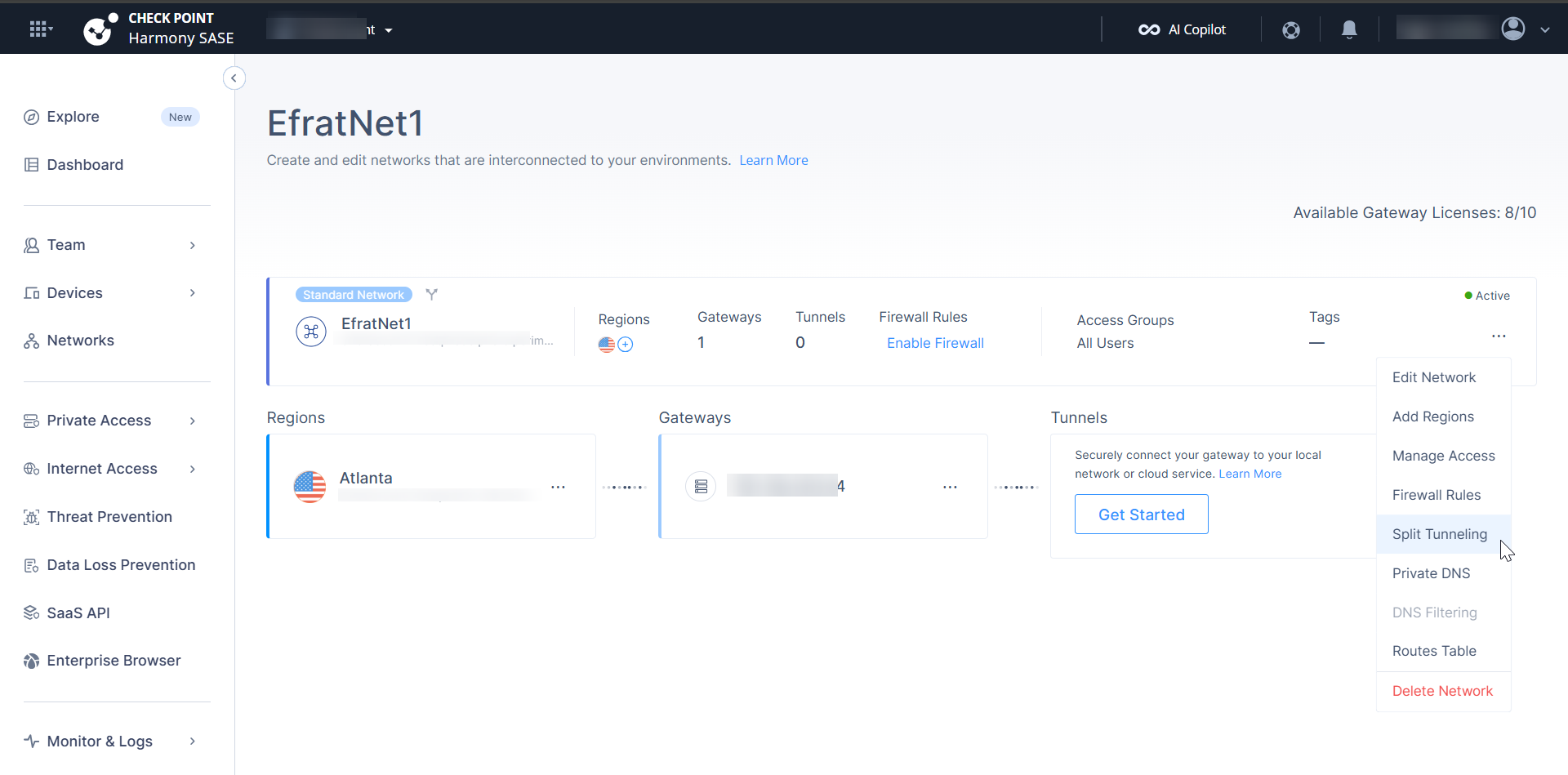 The Hybrid Split Tunneling window appears.
The Hybrid Split Tunneling window appears.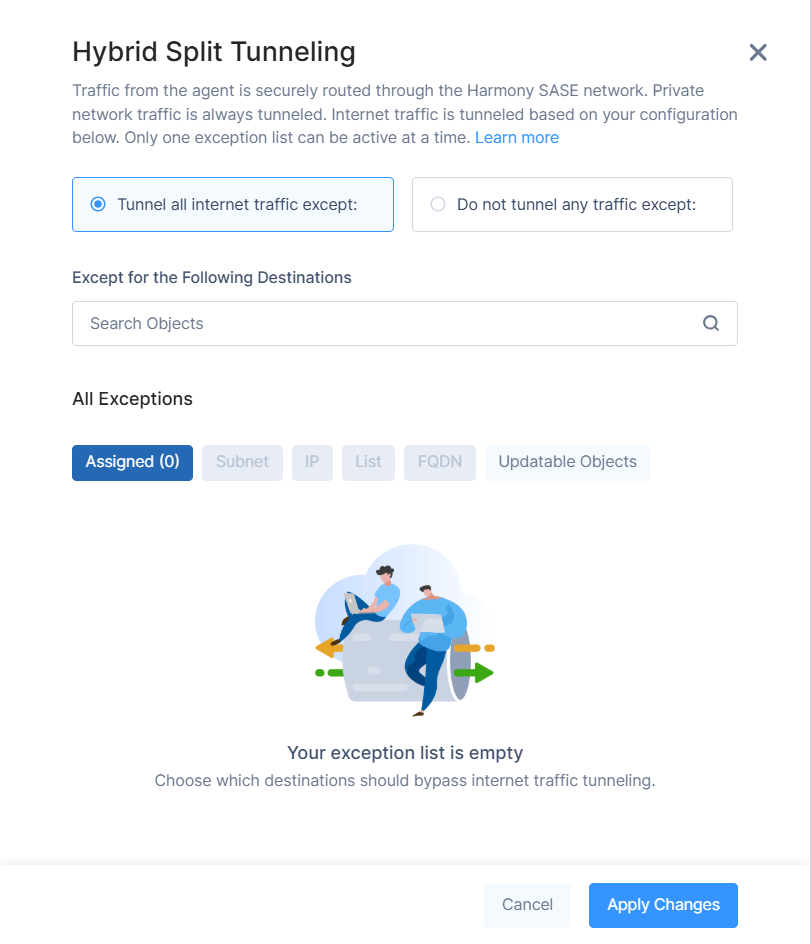
- Select one of these:
Tunnel all internet traffic: Routes all internet traffic through Check Point SASE, except the destinations you specify. These destinations bypass the tunnel.
Do not tunnel internet traffic: Routes only private network traffic through Check Point SASE. Internet traffic is sent directly to the internet, except the destinations you specify. These destinations are tunneled.
- In the Except for the Following Destinations, search for objects.
- In All Exceptions, select the required objects:
- Assigned: Displays the objects currently selected for this network.
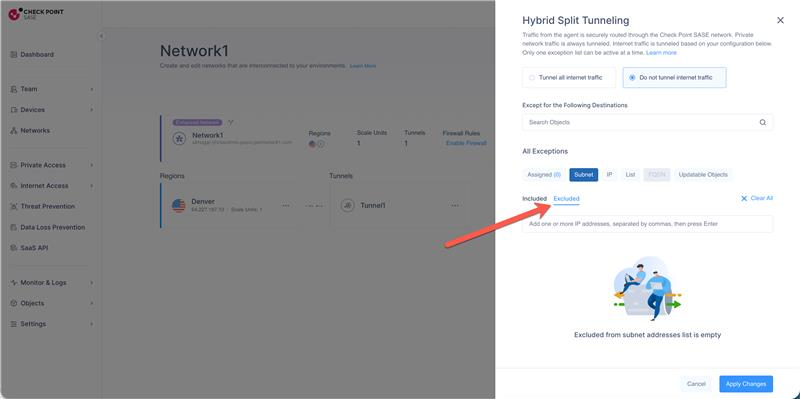
- Subnet: Select subnet-based destination objects.
When Do not tunnel internet traffic is selected, you can choose:- Included – Routes the selected subnets through the tunnel
- Excluded – Routes the selected subnets outside the tunnel
 Notes -
Notes -- The system validates excluded subnets against the included subnets list.
- Excluded subnets must be part of the included subnets.
- An administrator cannot add excluded subnets that are not included.
- The Included and Excluded options are available only for subnet-based destinations. In Tunnel all internet traffic, all specified destinations are automatically excluded.
- IP: Select individual IP address objects.
- List: Select predefined lists that contain multiple IPs, subnets, or FQDNs.
- FQDN: Select fully qualified domain name (FQDN) objects for domain-based split tunneling rules.
For more information on creating Subnet, IP, List, and FQDN objects, see Objects. - Updatable Objects: Select dynamic object groups that automatically update their IP ranges.
For more information, see Updatable Objects.Note -Microsoft Azure services, Amazon Web Services (AWS), and Geolocation-based Updatable Objects are not supported for Split Tunneling.
- Verify the selected objects under the Assigned tab.
Click Apply Changes.