Understanding DPC
Device Posture Checks ensure that only devices meeting specific security conditions access your network.
This adds an extra layer of security by verifying the device’s posture or security status before granting access to applications or data.
For example, administrators allow access to networks only from devices that comply with one or more of these policies:
- The presence of specific endpoint security software on the device.
- Whether a specific (authorization) file can be found on the device.
- Whether the device’s storage is encrypted.
- Whether a device holds the appropriate certificate (as defined by the administrator).
How to Set Up DPC
You can set device profiles per operating system. Each profile applies to a specific group, operating system, or both.
Check Point SASE applies Device Posture Check profiles to all Networks in your tenant.
To add a Device Posture Check profile:
- Navigate to Devices > Posture Check.
- Click (+) Add Profile.
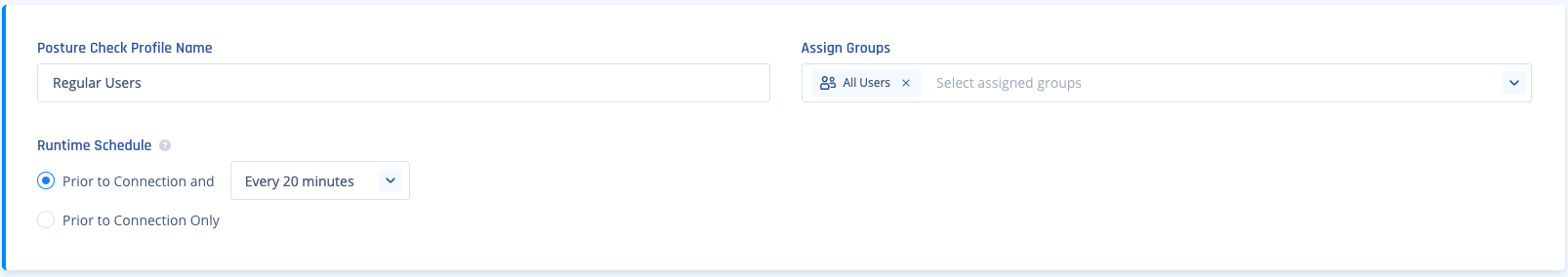
- Enter a Posture Check Profile Name.
- Select the Group(s) that should comply with the profile.
Check the All Users Group to apply the profile to all your Check Point SASE users.
- Select the suitable Runtime Schedule.
The system verifies the Device Posture Check periodically while a Member is connected or during every Network connection.
Define Posture Check per OS
Administrators define different profiles or requirements for each operating system within the same profile or create separate profiles for each OS.
Each OS profile includes one or more rules that devices must meet to access Networks.
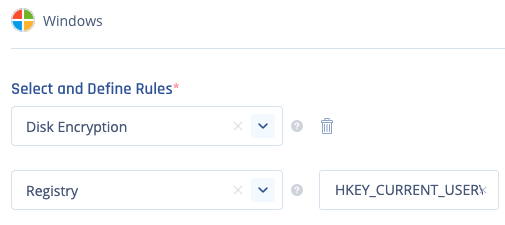
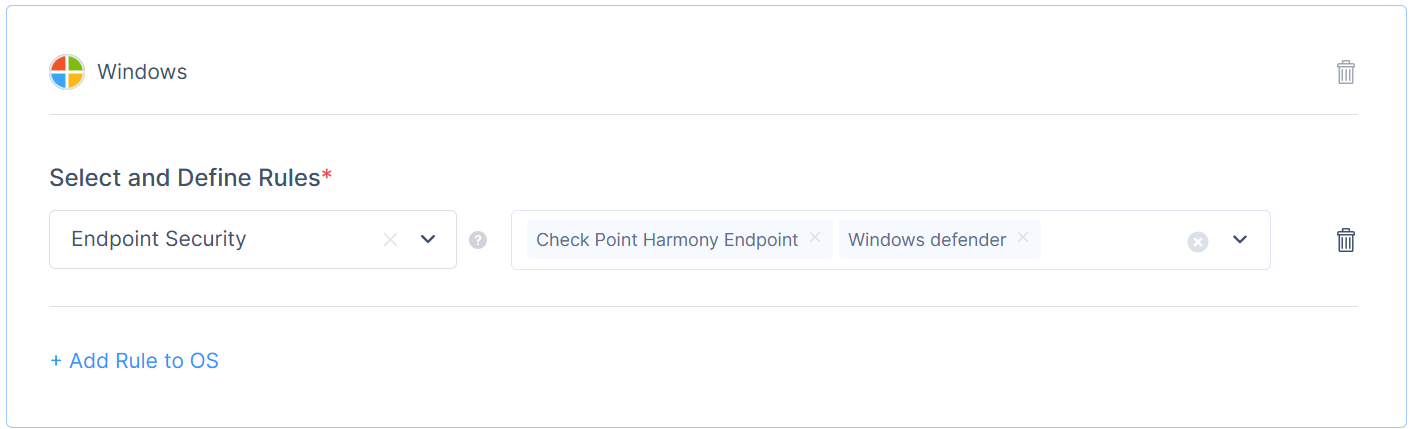
Windows:
- Click Add OS to Profile
- Select and Define Rules
You can pick one of these options:
Endpoint Security - The Check Point SASE agent verifies the presence of the selected Endpoint Security application.
File-Exists - The Check Point SASE agent verifies the presence of a specific file in a specific path.
Disk Encryption - The Check Point SASE agent checks if the OS hard drive is encrypted.
Certificate Subject - The Check Point SASE agent verifies that a specific certificate's subject is installed on the device (in the local Windows CA store or macOS Keychain).
Certificate Issuer & CA - The Check Point SASE Agent verifies that the device holds the appropriate certificate. Supports PEM certificates only. The maximum file size allowed is 50KB. Supported from agent version 12.0. Optionally, select Verify matching private key on device to perform an additional check. This ensures the certificate is valid, matches the expected issuer, and that the corresponding private key is present on the device.
Process Running - The Check Point SASE agent verifies that a specified process is running in the background. This can also be used to check endpoint security solutions that are not pre-defined under the Endpoint Security category.
Registry - The Check Point SASE agent verify a specific registry key.
(Example: HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Tcpip\Parameters\New Key)
Windows Security Center - The Check Point SASE agent verifies the status of the selected Firewall, Endpoint Security, or Windows Security Center is showing as "Good".
Active Directory Association - The Check Point SASE agent verifies the user's logon_domain matches what is specified in the rule (case-insensitive). Ten domains are supported with an OR statement.
Operating System version - The Check Point SASE agent verifies that the device is using an accepted version (equal to and/or higher than).
- Click on Add Rule to OS (if needed)
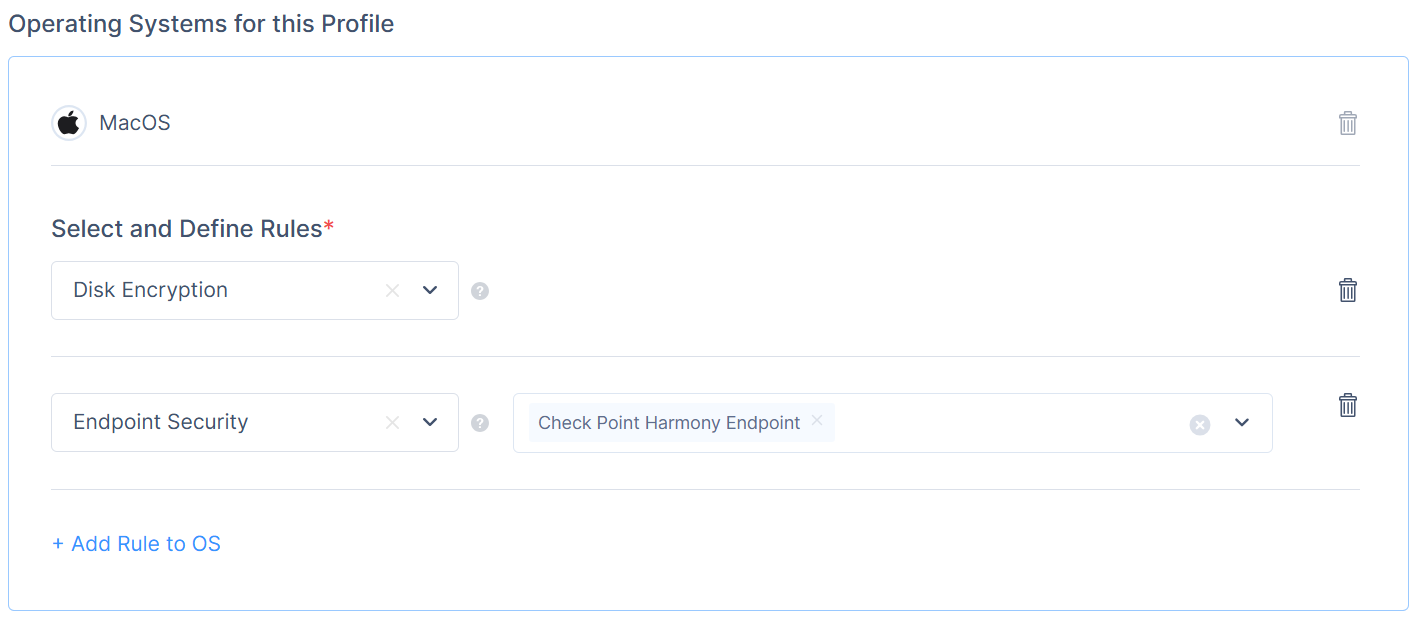
MacOS:
- Click Add OS to Profile
- Select and Define Rules
You can pick one of these options:
Endpoint Security - The Check Point SASE agent checks for the selected Endpoint Security application.
File-Exists - The Check Point SASE agent checks for a specific file in a specific path.
Certificate Subject - The Check Point SASE agent verifies that a specific certificate's subject is installed on the device (in the local Windows CA store or macOS Keychain).
Certificate Issuer & CA - The Check Point SASE Agent verifies that the device holds the appropriate certificate. Supports PEM certificates only. The maximum file size allowed is 50KB. Supported from agent version 12.0. Optionally, you can select the Verify matching private key on device checkbox to perform an additional check. This verifies that the certificate is valid, matches the expected issuer, and that the corresponding private key is present on the device.
Disk Encryption - The Check Point SASE agent checks if the OS hard drive is encrypted.
Process Running - The Check Point SASE agent checks if a specified process is running in the background. This also checks endpoint security solutions that are not pre-defined under the Endpoint Security category.
Certificate - The Check Point SASE agent checks if a specific certificate is installed on the device (Mac Keychain).
Operating System version - The Check Point SASE agent checks if the device uses an accepted version (equal to and/or higher than).
Active Directory Association - The Check Point SASE agent checks if the user's logon_domain matches the specified rule (case-insensitive). Ten domains are supported with an OR statement.
- Click on Add Rule to OS (if needed)
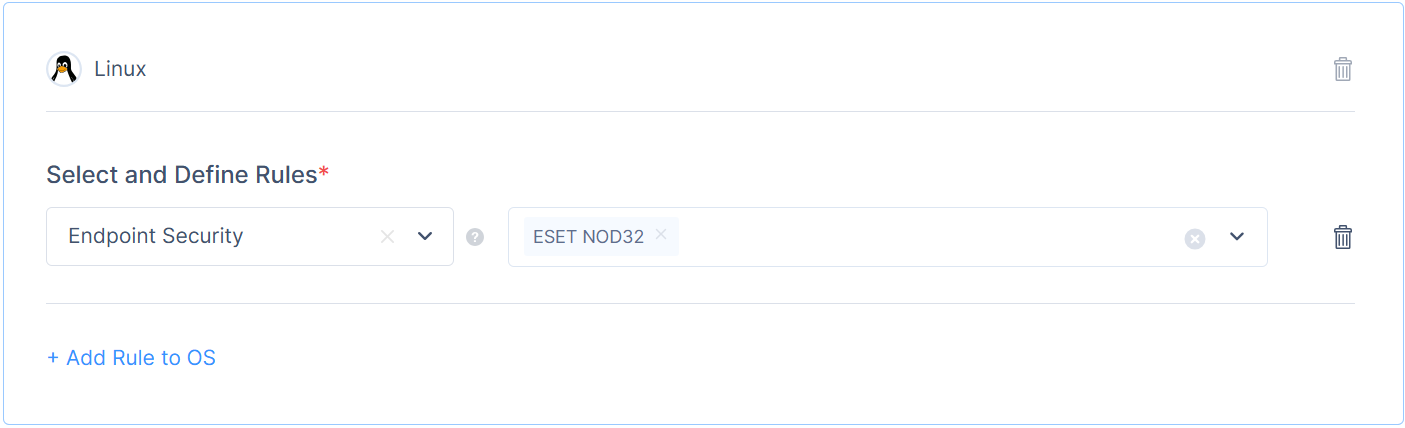
Linux:
- Click Add OS to Profile
- Select and Define Rules
You can pick one of these options:
Endpoint Security - The Check Point SASE agent checks for the selected Endpoint Security application.
File-Exists - The Check Point SASE agent checks for a specific file in a specific path.
Process Running - The Check Point SASE agent checks if a specified process is running in the background. This also checks endpoint security solutions that are not pre-defined under the Endpoint Security category.
- Click on Add Rule to OS (if needed)
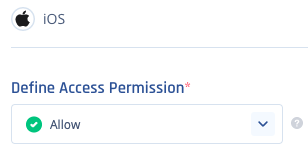
iOS:
- Click Add OS to Profile
- Select and Define Rules
You can pick one of these options:
Allow - Mobile devices using the Check Point SASE application can access Networks.
Deny - Mobile devices using the Check Point SASE application cannot access Networks.
- Click on Add Rule to OS (if needed)
Android / Chromebook:
- Click Add OS to Profile
- Select and Define Rules
You can pick one of these options:
Allow - Mobile devices using the Check Point SASE application can access Networks.
Allow Chromebook Only - Chromebooks using the Check Point SASE application can access Networks, while devices running Android cannot.
Deny - Mobile devices using the Check Point SASE application cannot access Networks.
- Click on Add Rule to OS (if needed)
.png)
Recommendations
- Conduct a risk assessment to determine which posture checks are most critical for your organization.
- Regularly update your posture check settings to align with evolving security policies.
Troubleshooting
If you encounter issues during or after the setup, try reviewing your settings to ensure everything matches the instructions. In particular, check the IP addresses and other details you entered during setup. If issues persist, please consult our dedicated support.
Support Contacts
If you have any difficulties or questions, don't hesitate to contact Check Point SASE's support team. We offer 24/7 chat support on our website at sase.checkpoint.com, or you can email us at sase-support@checkpoint.com. We're here to assist you and ensure your VPN tunnel setup is a success