Introduction
This guide explains how to enable users to log in using a Microsoft Entra ID (formerly Azure Active Directory) account, either from your company or from external directories.
The process involves registering your application through the Microsoft Azure portal
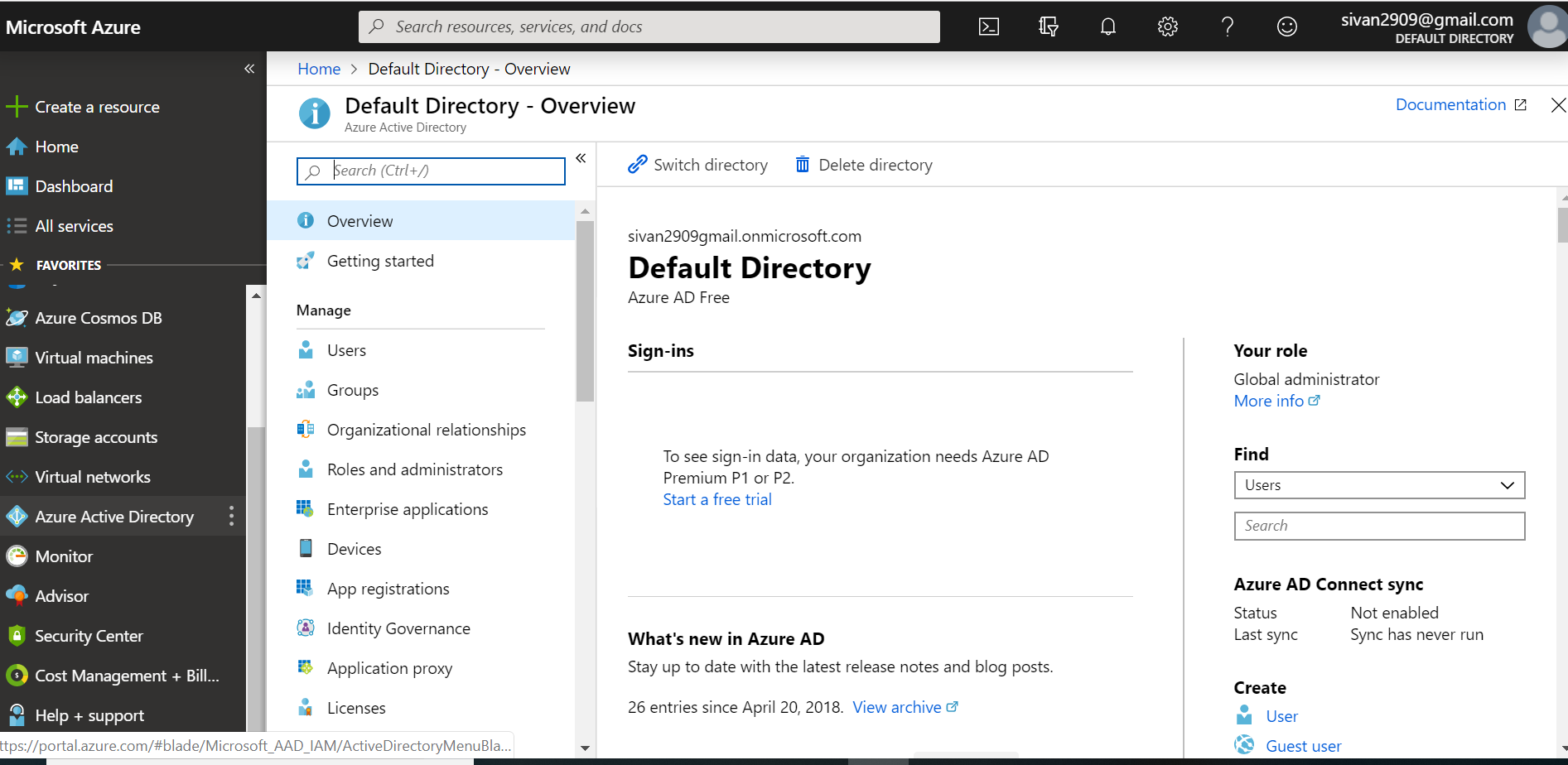
If you have an Office 365 account, you can use the account's Microsoft Entra ID instance instead of creating a new one. To find your Office 365 account's Microsoft Entra ID instance:
- Sign in to Office 365.
- Navigate to the Office 365 Admin Center.
- Open the Admin centers menu options located on the left menu.
- Select Azure AD.
This will take you to the Admin Center of the Entra IDinstance backing your Office 365 account.
Follow the steps below to connect your Check Point SASE Account to Azure Active Directory (images below): - Create a new application.
- Configure the permissions.
- Allow access from external organizations (optional).
- Create the key.
- Configure Reply URLs.
- Configure Check Point SASE IDP connection.
Steps
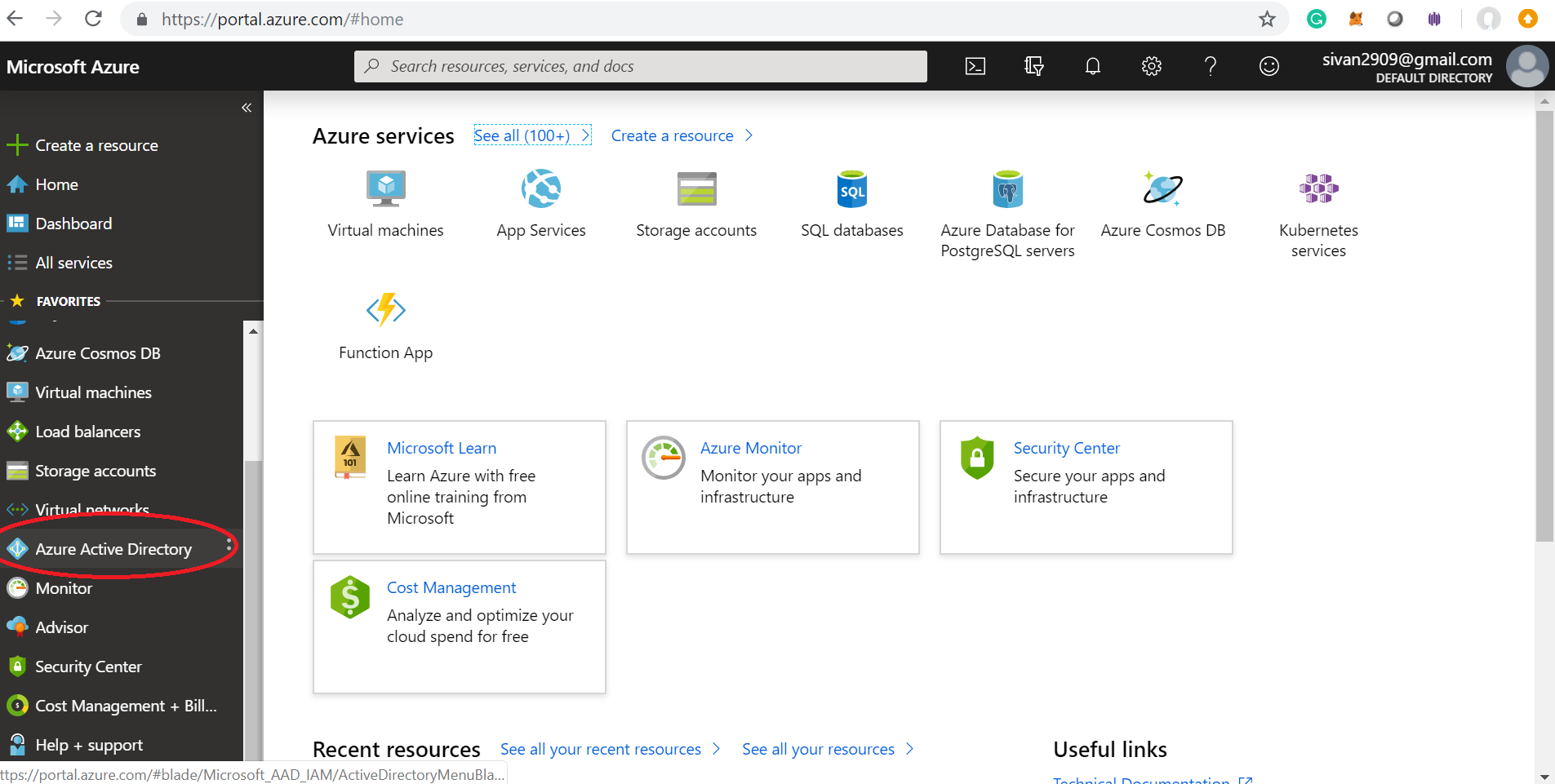
- Log in to Microsoft Azure and choose Azure Active Directory from the sidebar.
ֿ
2. Under Manage, select App registrations.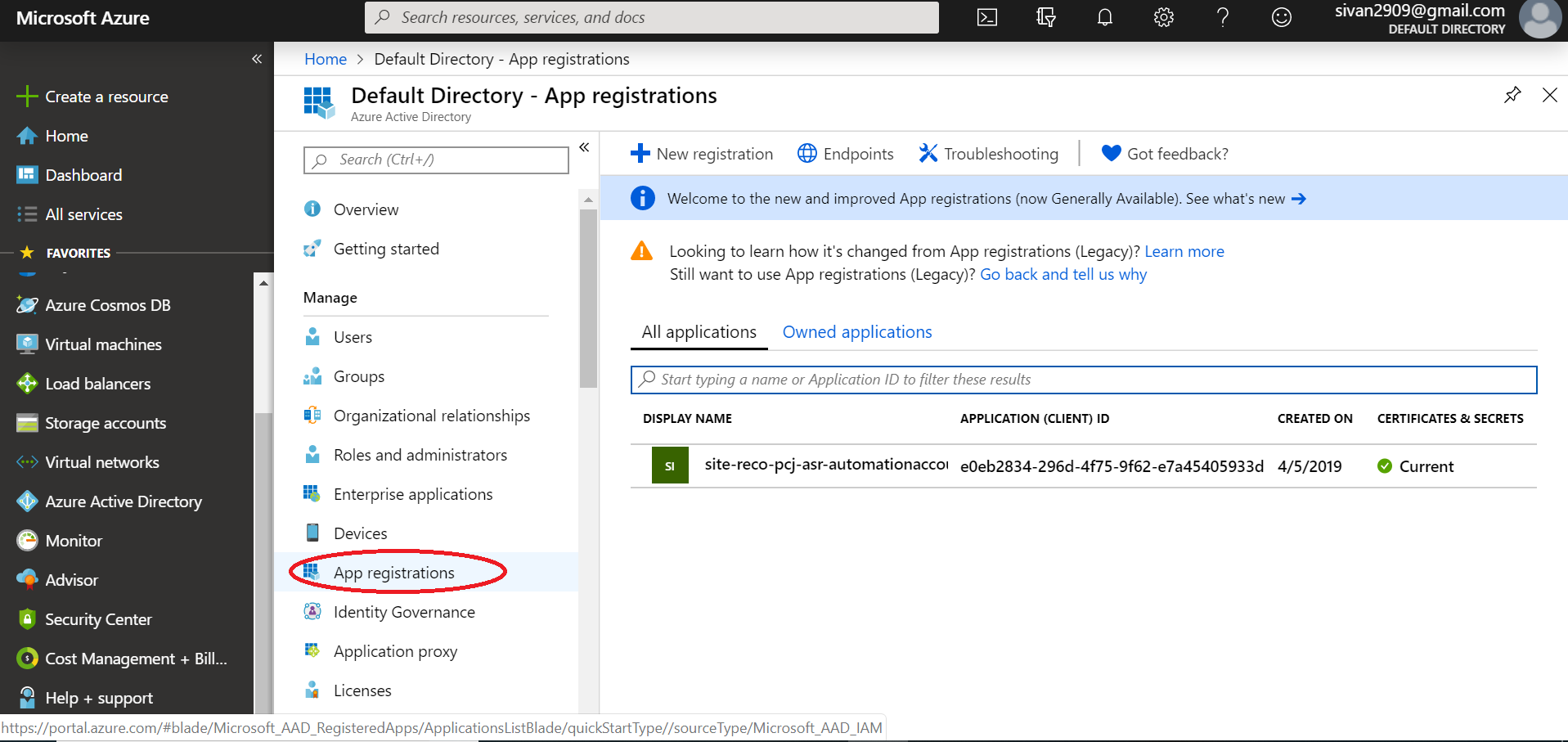
3. Select New Registration to add a new application.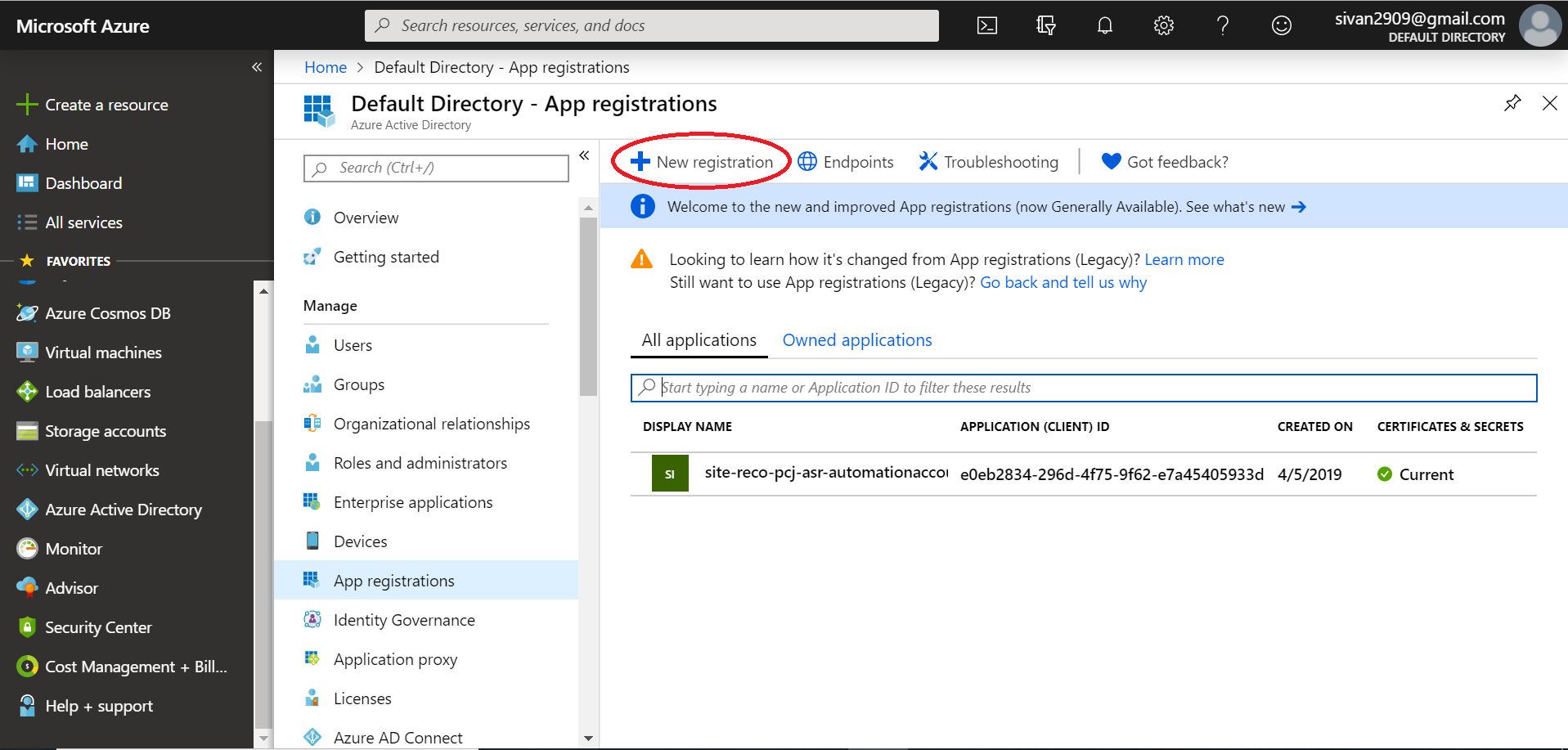
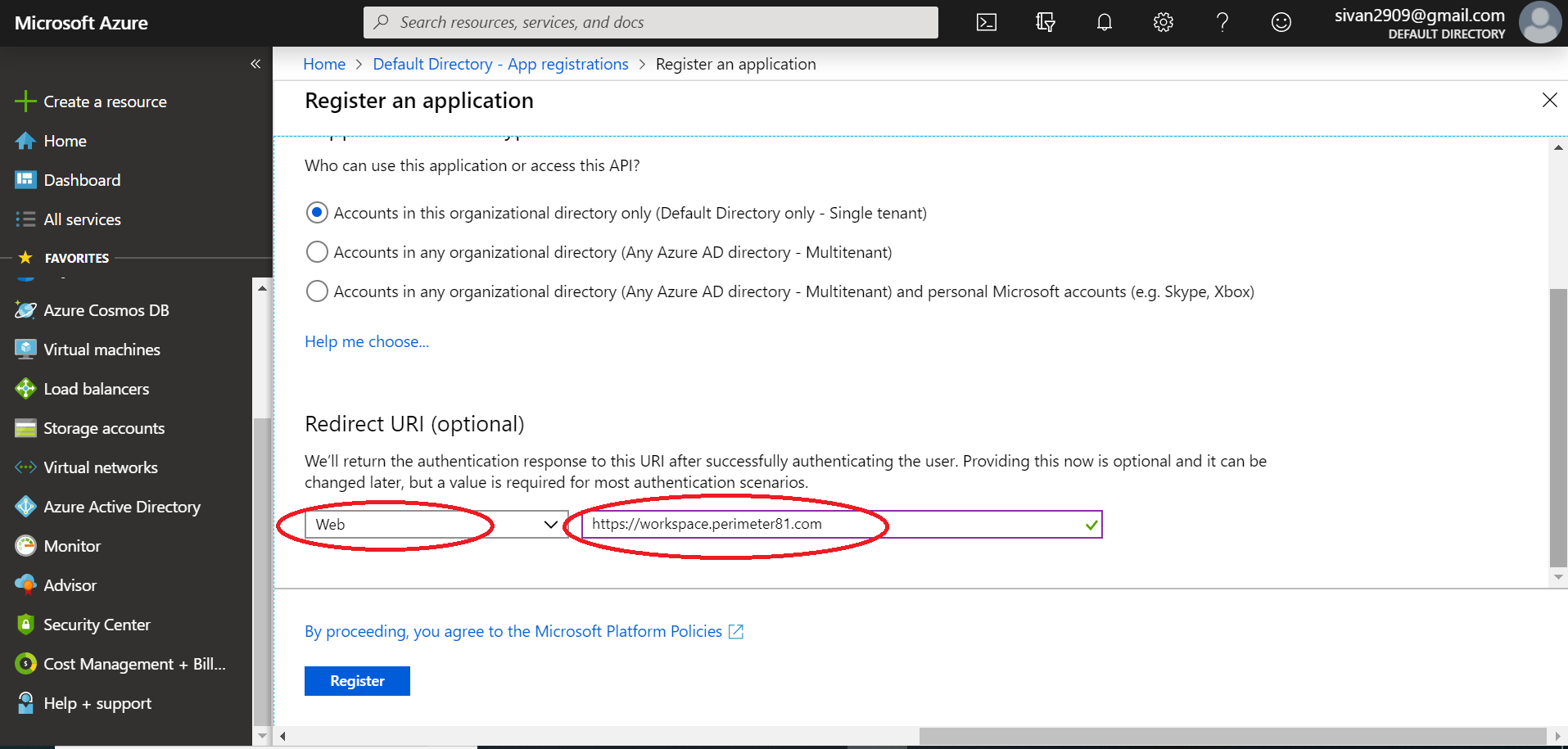
4. Enter the name "Check Point SASE" for the application, select Web app/API as the Application Type, and for Sign-on URL enter your application URL with your workspace name:
- US based platform - https://workspace.perimeter81.com
- EU based platform - https://workspace.eu.sase.checkpoint.com
- AU based platform - https://workspace.au.sase.checkpoint.com
- IN based platform - https://workspace.in.sase.checkpoint.com
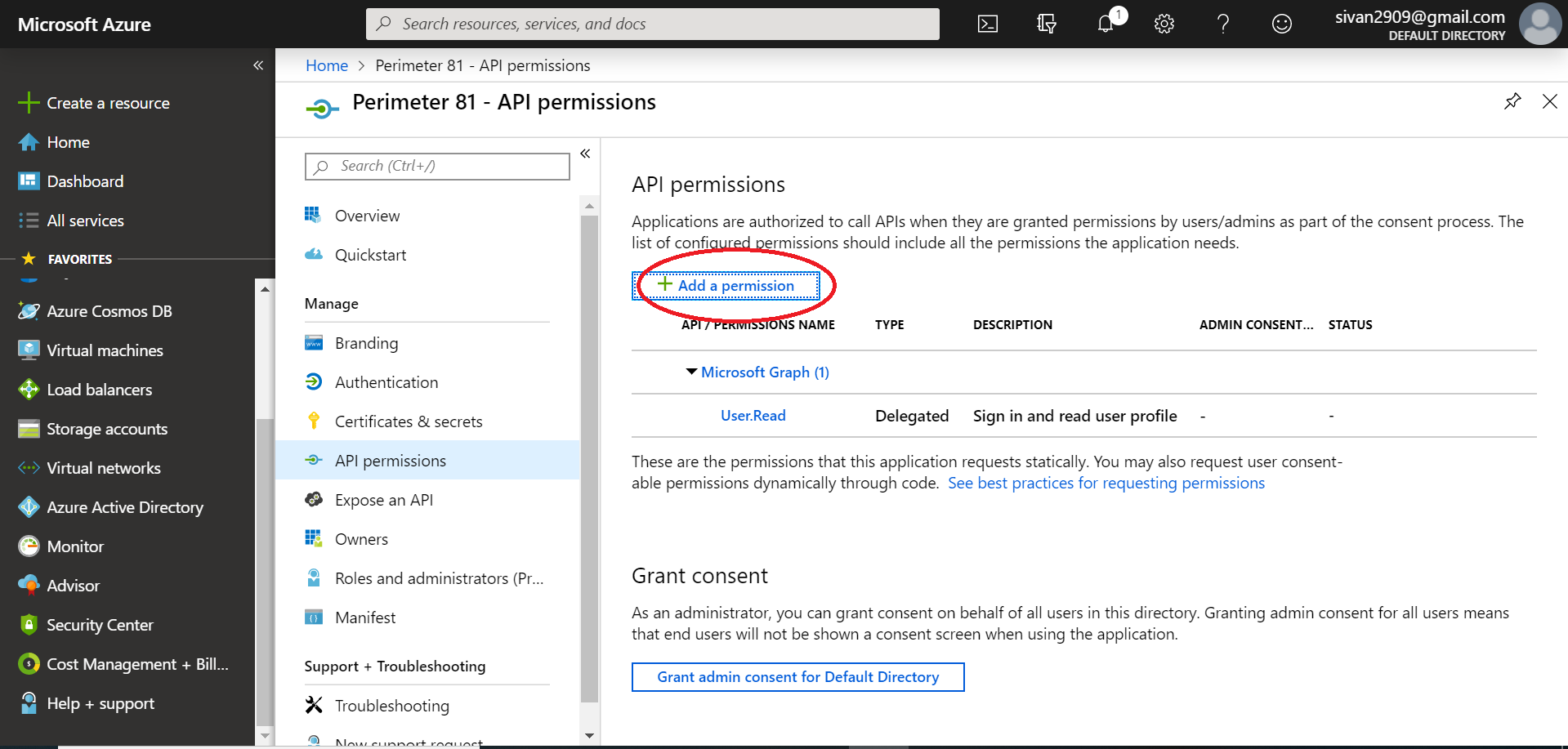
Configuring the permissions
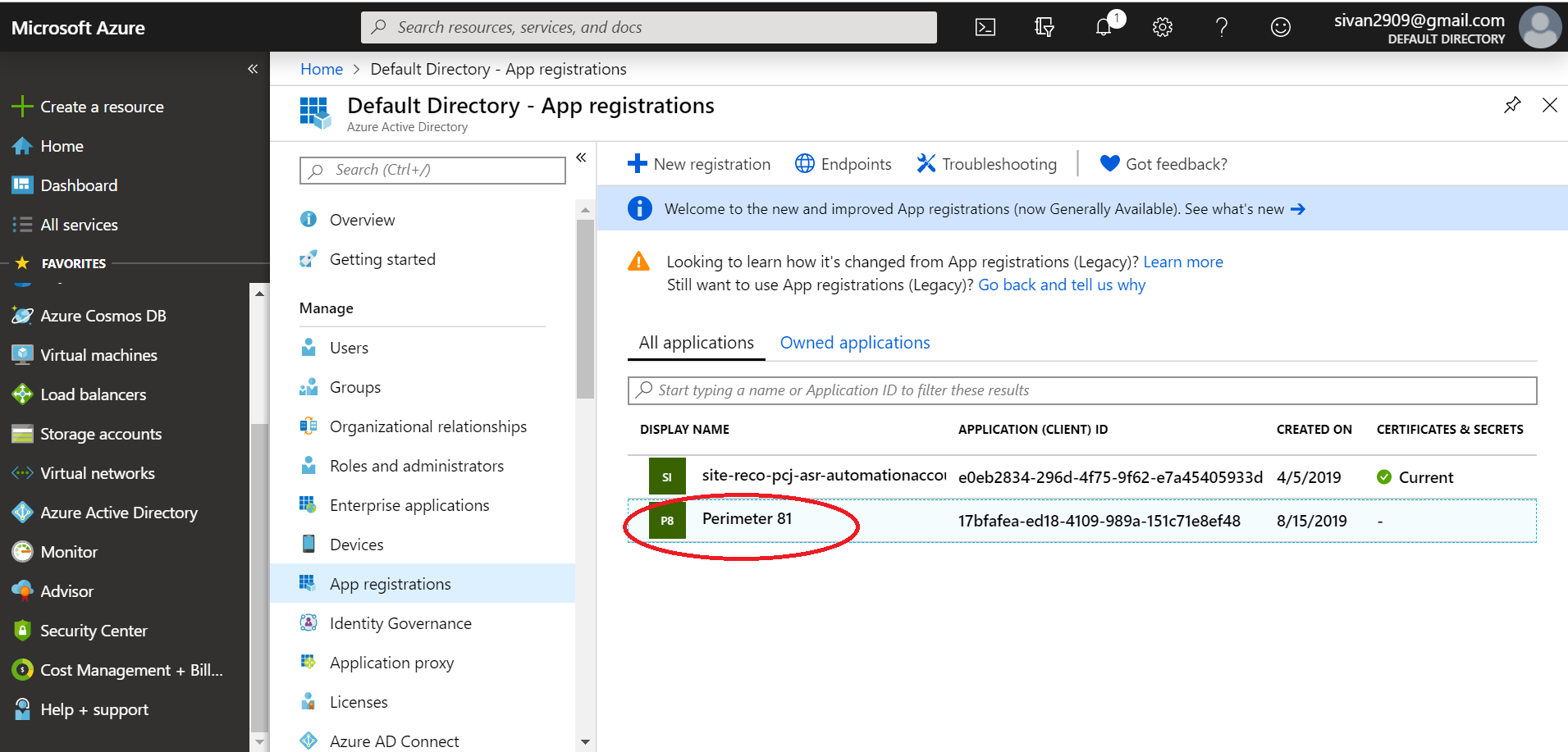
- Once the application has been created, you will have to configure the permissions. Select the name of the application Check Point SASE to open the Settings section.
- Select API permissions.
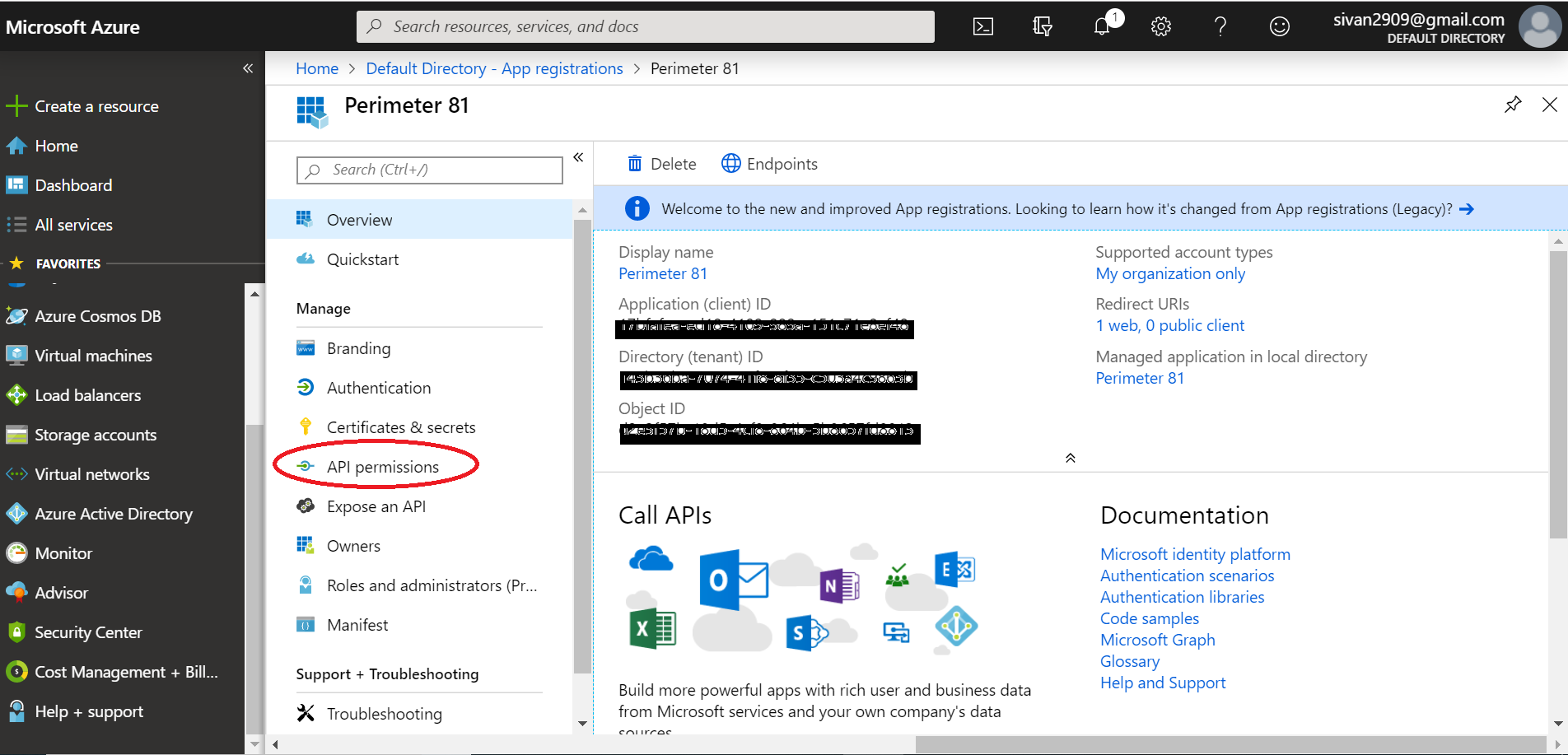
- Select Add a permission.
- Select Microsoft APIs and choose Microsoft Graph to change the access level.
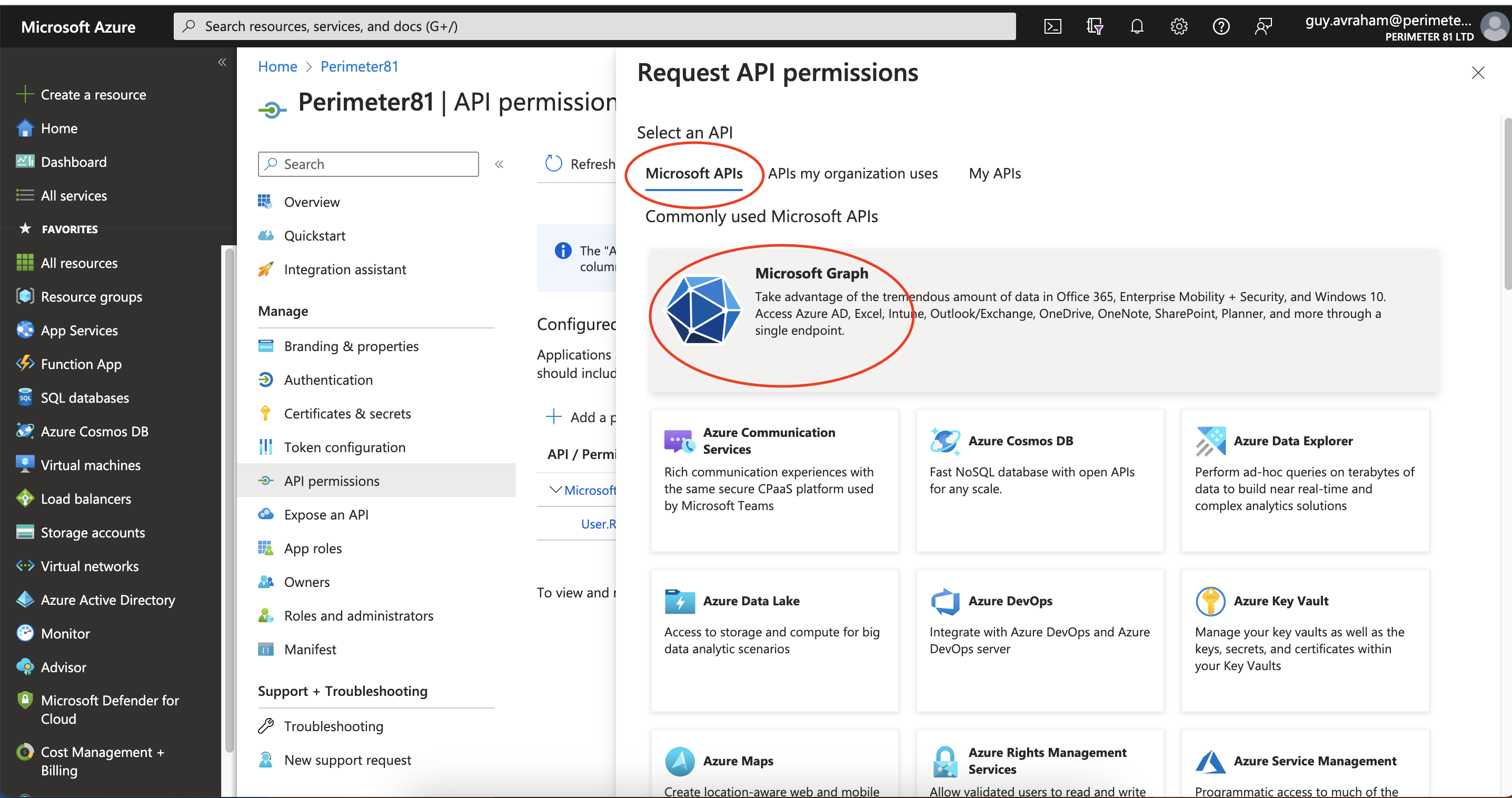
The following page displays: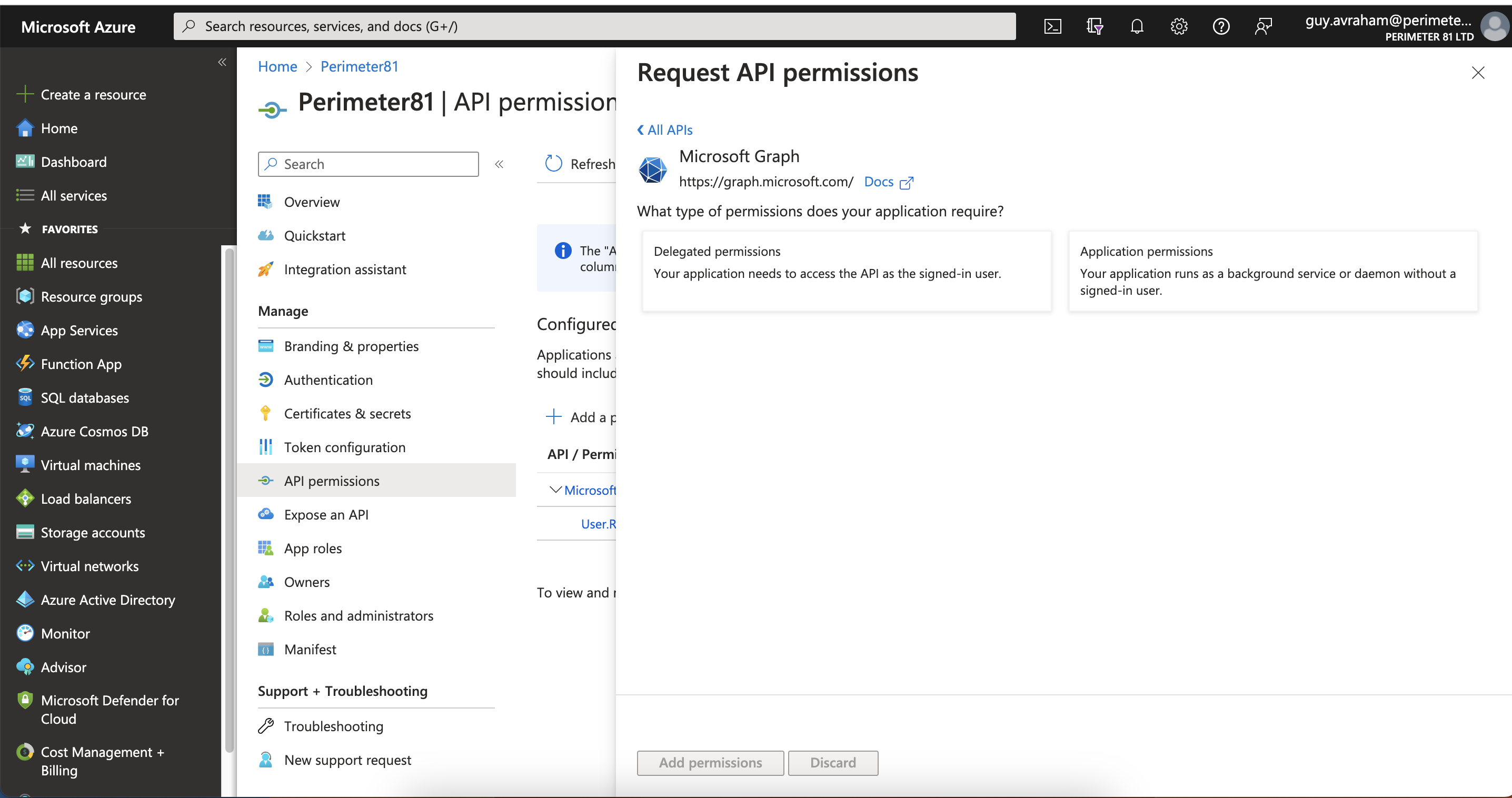
5. The next step is to modify permissions so your app can read the directory. Under Delegated permissions, check next to Sign in and read user profile and Read directory data.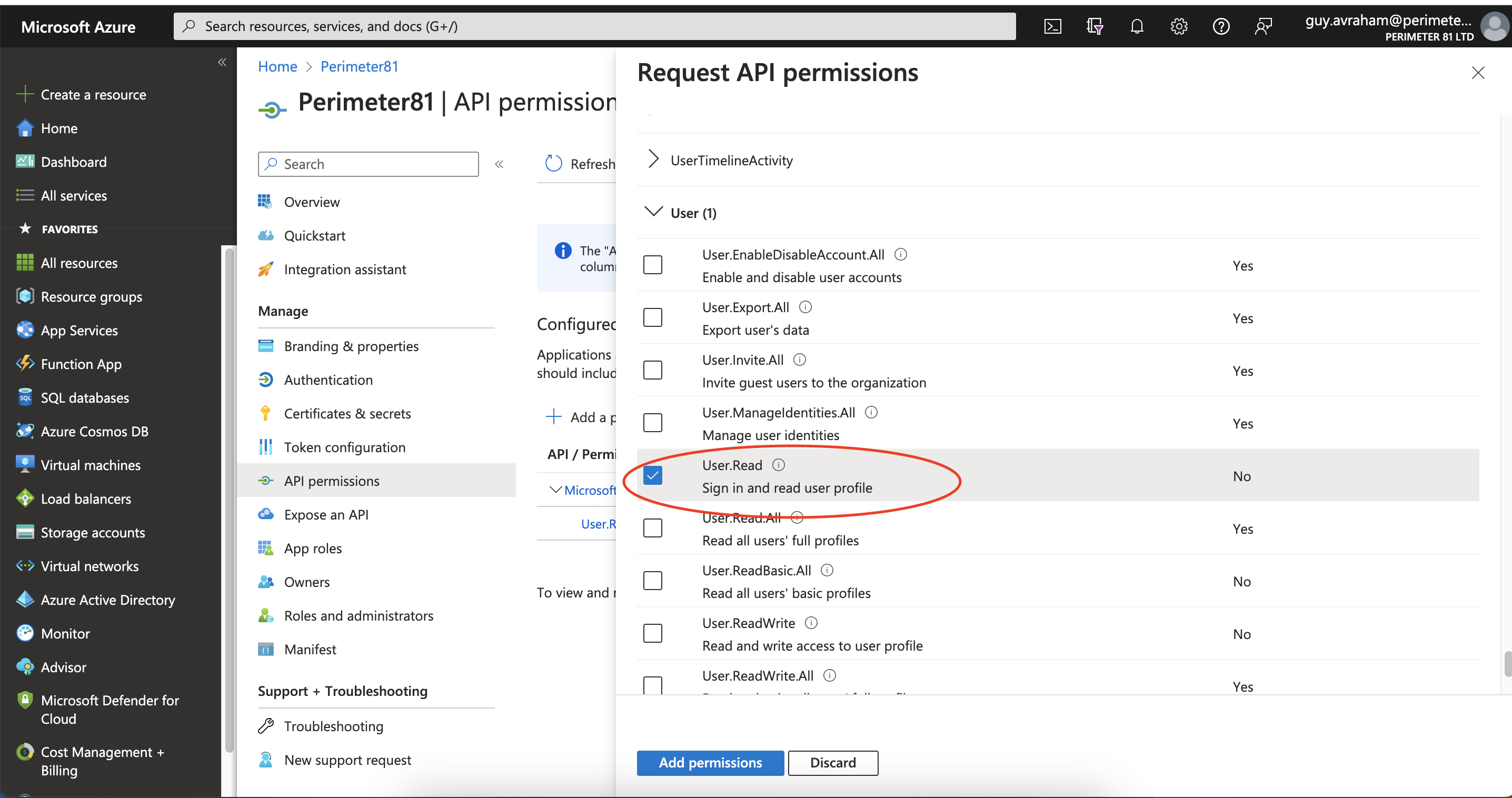
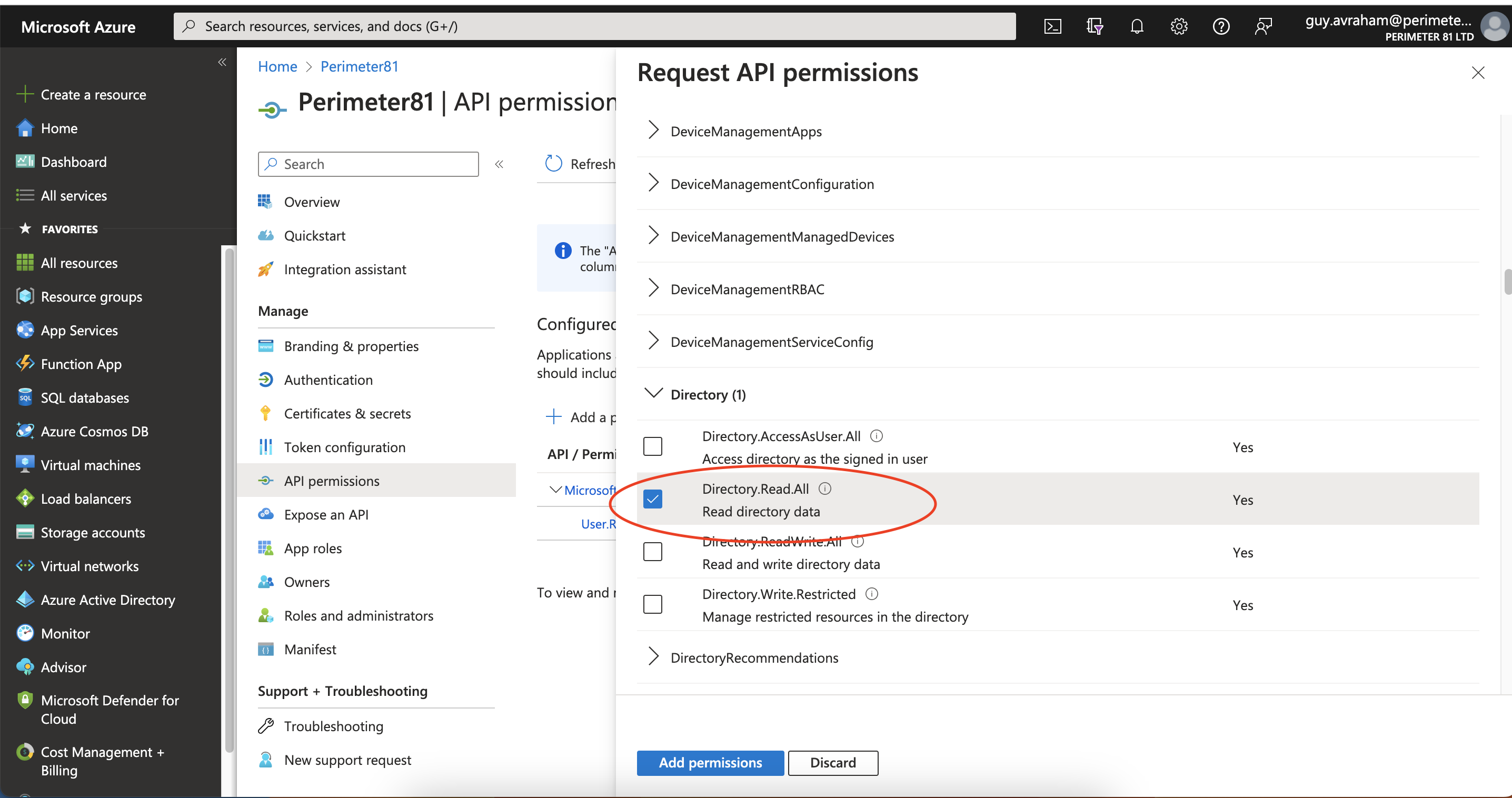 6. Grant Admin Consent if requested.
6. Grant Admin Consent if requested.
Support user groups
- If you want to enable user group support you will need to enable the following permissions:
- Application Permissions: Read directory data
- Delegated Permissions: Access the directory as the signed-in user.
- Select Save at the top to save these changes.
- Grant Admin Consent if requested.
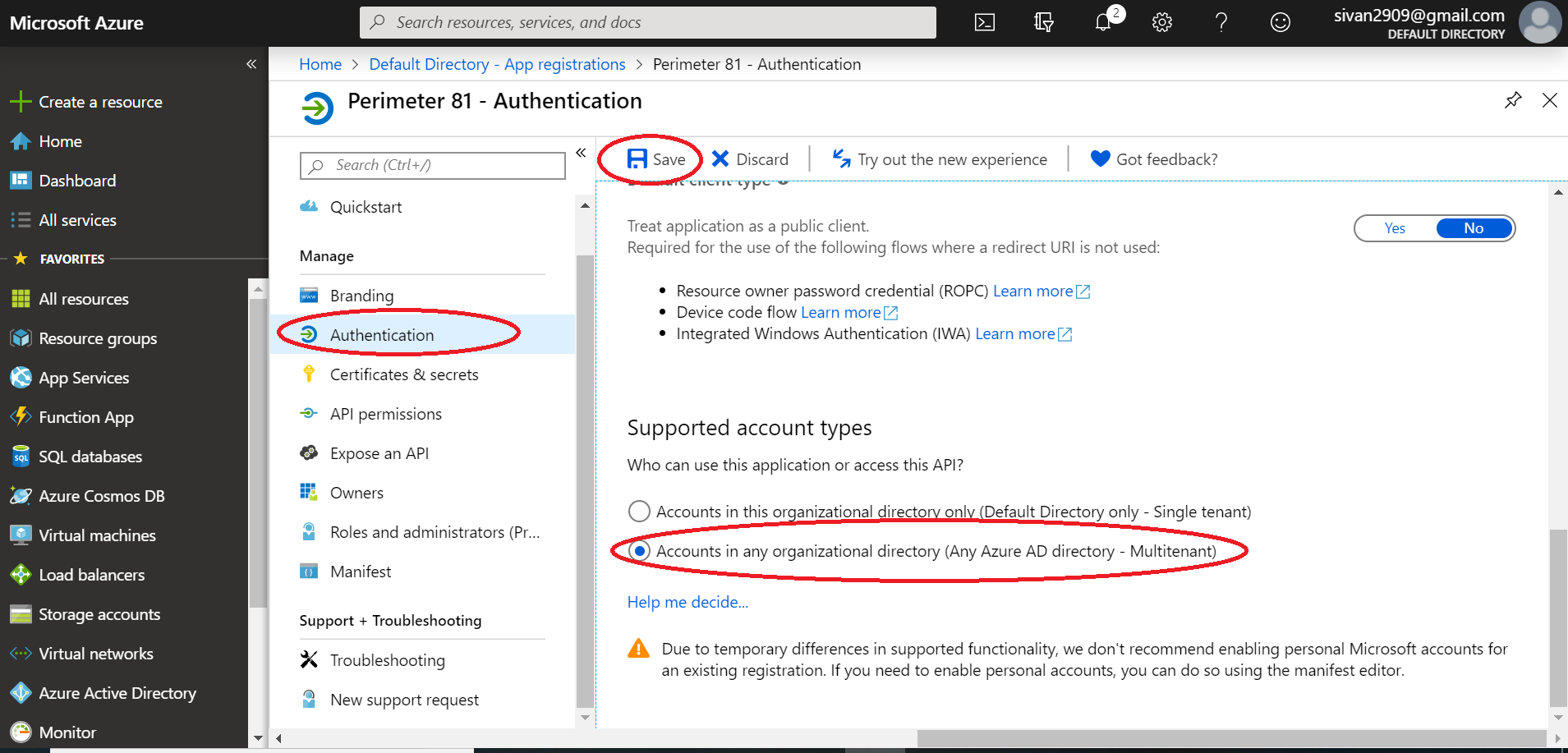
Allowing access from external organizations (optional)
- If you want to allow users from external organizations (such as other Entra IDs) to log in, you will need to enable the Multi-Tenant option for this application. In the Authentication section, choose the Multi-tenant option.
- Select Save at the top to save these changes.
- Grant Admin Consent if requested.
Configuring Reply URLs
- Next, you need to ensure that your Auth0 callback URL is listed in the allowed reply URLs for the created application.
- Navigate to Azure Active Directory, then Apps registrations and select the Check Point SASE app.
- Select Authentication, go to Redirect URLs and add this link:
- For US based platform: https://auth.perimeter81.com/login/callback
- For EU based platform: https://auth.eu.sase.checkpoint.com/login/callback
- For AU based platform: https://auth.au.sase.checkpoint.com/login/callback
- For IN based platform: https://auth.in.sase.checkpoint.com/login/callback
- Audience URI (SP Entity ID):
- For US based platform: urn:auth0:perimeter81:{{WORKSPACE}}-oc
- For EU based platform: urn:auth0:eu-sase-checkpoint:{{WORKSPACE}}-oc
- For AU based platform: urn:auth0:au-sase-checkpoint:{{WORKSPACE}}-oc
- For IN based platform: urn:auth0:in-sase-checkpoint:{{WORKSPACE}}-oc
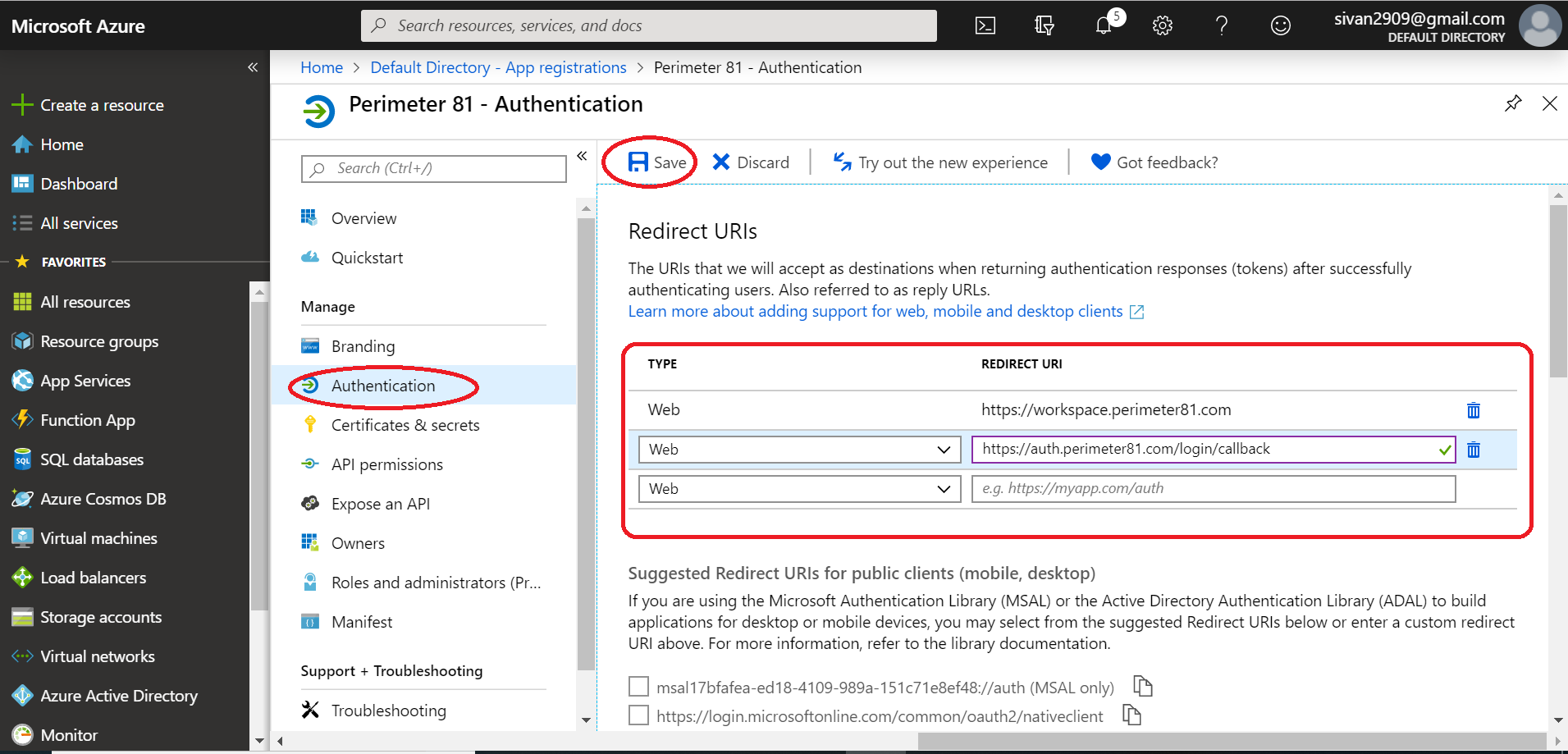
- Select Save.
Configuring the key
- You will need to create a key (secret password) that will be used as the Client Secret in the Check Point SASE IDP connection. Select Certificates and secrets from the Application menu.
- Click + New Client Secret
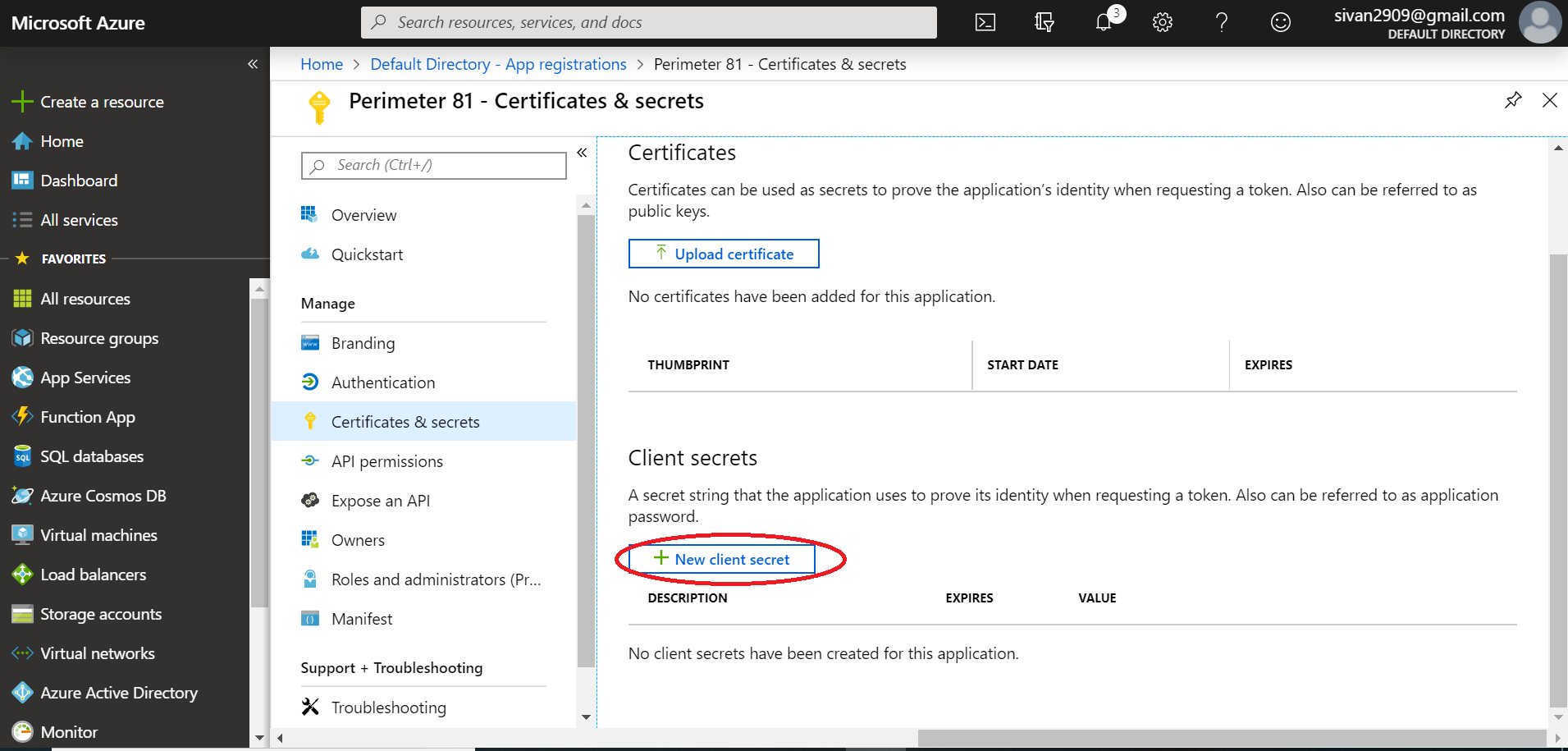
- Enter a name for the key and choose the desired duration.
- This is an expiring key, make sure to record the expiration date in your calendar, as you will need to renew the key (get a new one) before that day to ensure users don't experience a service interruption.
- Select Add and the key will be displayed.
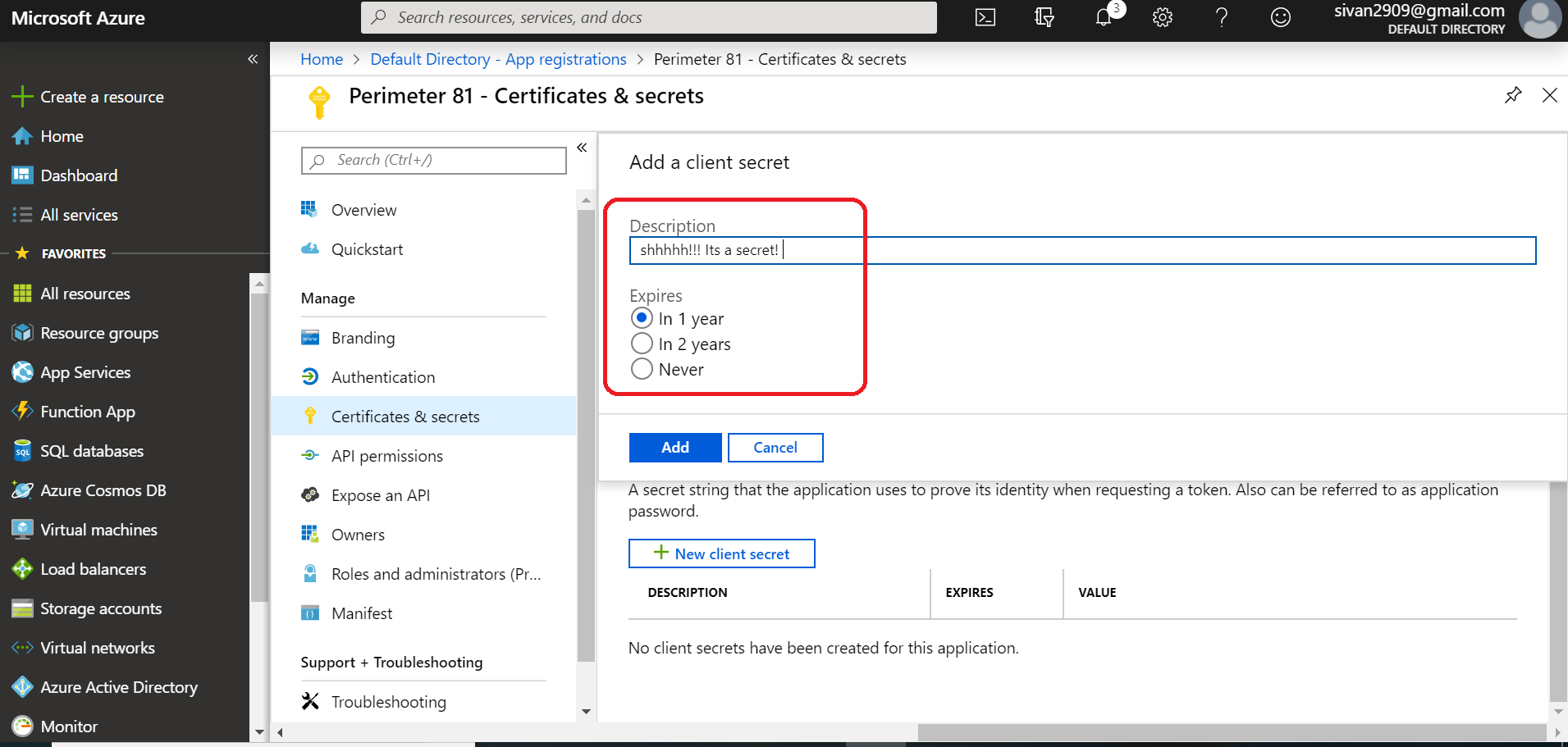
- Make sure to copy the Secret Value field of this key before leaving this screen. Otherwise, you may need to create a new key.
- This will later be pasted into the Client Secret field in the Check Point SASE Admin console.
- You do not need to copy the "Secret ID"
.png)
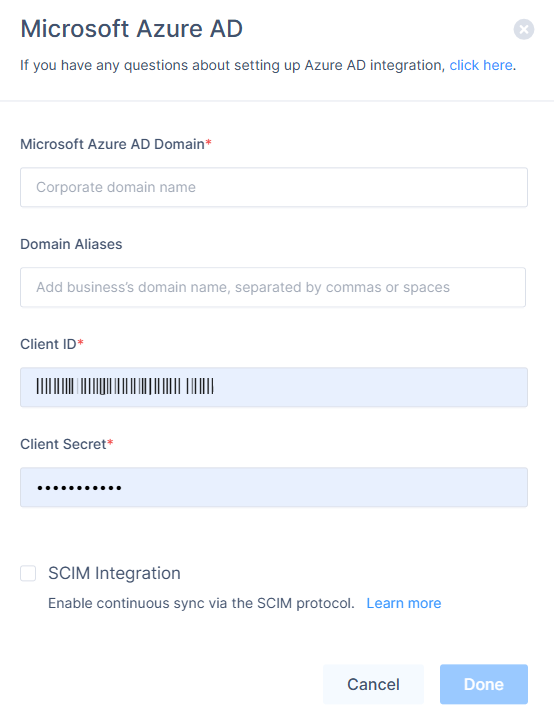
Configuring IDP connection
- Log in to your Check Point SASE Management Platform, navigate to Settings, and then IdentityProviders.
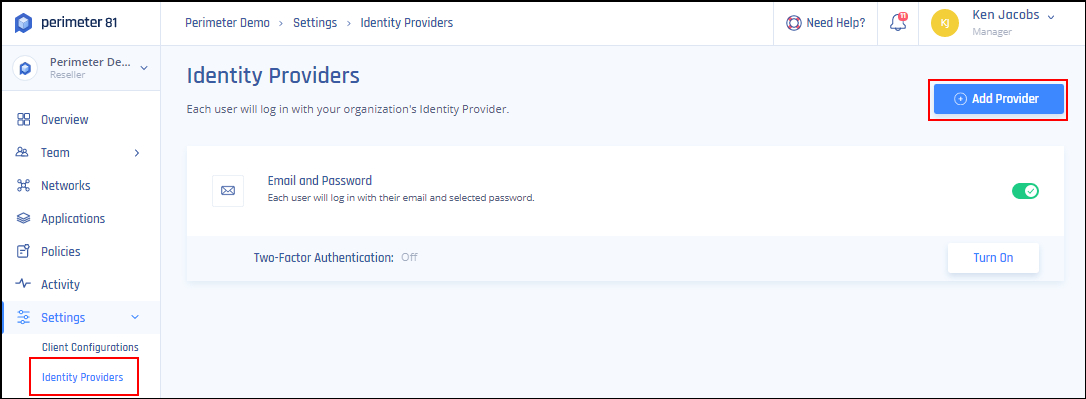
- Select + Add Provider.
- Choose Microsoft Azure AD.
- Fill in Microsoft Azure AD Domain (your domain - for example harmonysase.com), Domain Aliases (optional), Client ID, Client Secret and select the SCIM Integration checkbox.
- Under Domain set the name of the Microsoft Azure AD Domain and under Domain Aliases insert any email domain that you may be using.
- The Client ID value is stored as the Application ID in Microsoft Entra ID, you can copy that from the "Overview" section.
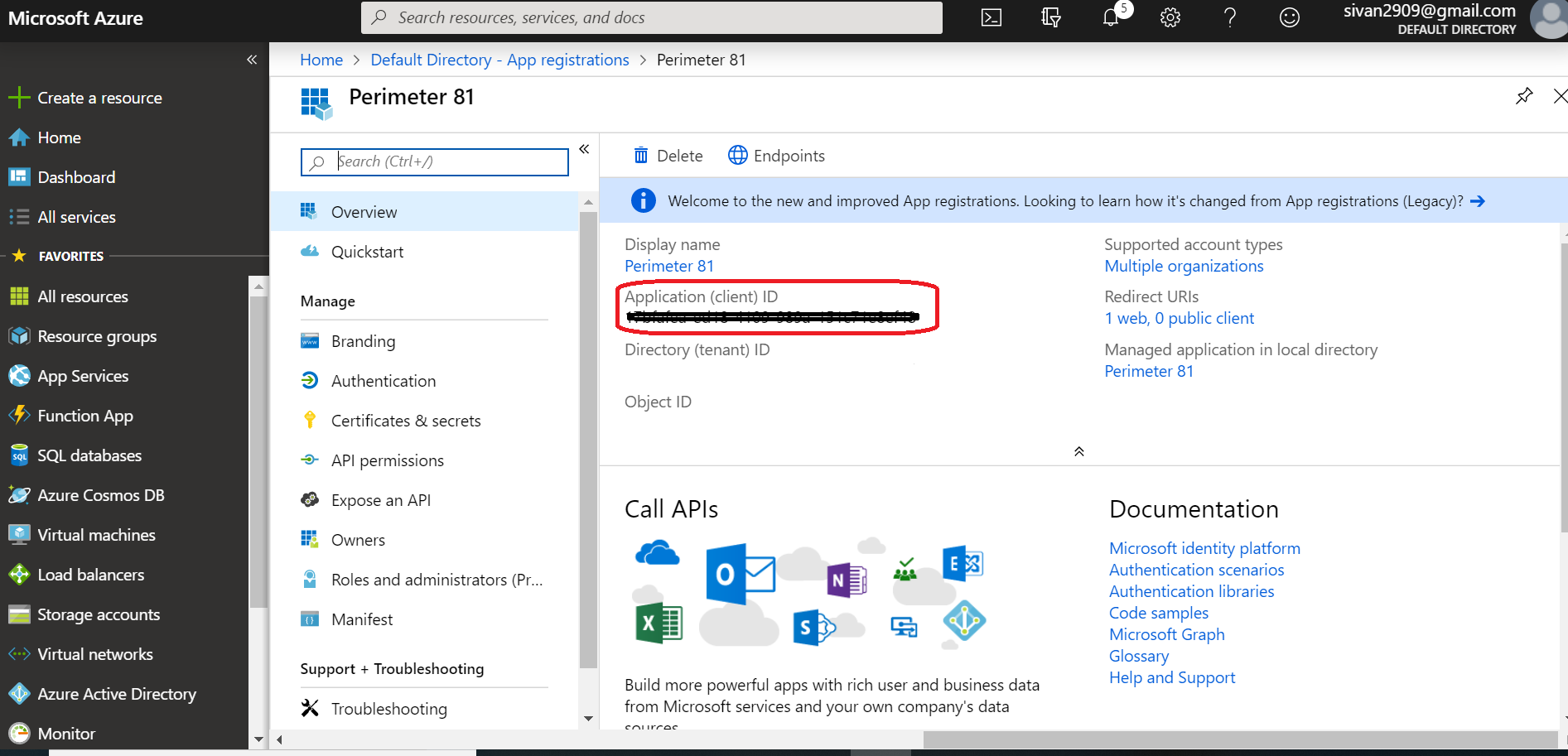
- In the Client Secret field, enter the value that was shown for the key when you created it in the previous step.
- Click Save.
Recommendations
- Assign access to users or groups. For the Microsoft Entra ID free edition, you might need to select individual users instead of groups.
- Ensure placeholders like YOURWORKSPACEHERE are replaced with your actual workspace name.
- Periodically review your Microsoft Entra ID configuration settings to ensure alignment with any updates or changes in the Check Point SASE platform
Troubleshooting
If you encounter issues during or after the setup, try reviewing your settings to ensure everything matches the instructions. In particular, check the IP addresses and other details you entered during setup. If issues persist, please consult our dedicated support.
Support Contacts
If you have any difficulties or questions, don't hesitate to contact Check Point SASE's support team. We offer 24/7 chat support on our website at sase.checkpoint.com, or you can email us at sase-support@checkpoint.com. We're here to assist you and ensure your VPN tunnel setup is a success